Leaked pentagon documents ukraine discord – Leaked Pentagon documents detailing the Ukraine conflict, initially shared within a Discord server, have ignited a firestorm. This explosive leak, revealing sensitive intelligence and strategic assessments, has sent shockwaves through the international community, raising serious questions about national security, the integrity of intelligence gathering, and the power of online platforms to disseminate sensitive information. The ripple effects of this breach extend far beyond the digital realm, impacting geopolitical strategies and public trust.
From the seemingly innocuous online chatroom to global headlines, the journey of these documents unveils a complex narrative of human error, online anonymity, and the unpredictable nature of information warfare in the digital age. We delve into the origins of the leak, the content’s implications, and the legal and security ramifications, exploring the human element behind the headlines and the broader consequences for global politics.
The Source and Spread of the Documents
The leak of highly sensitive Pentagon documents, initially surfacing on a niche Discord server, represents a significant intelligence breach with far-reaching consequences. Understanding the source, dissemination methods, and subsequent escalation is crucial to grasping the gravity of this situation and preventing future occurrences. The investigation is ongoing, but several key aspects of the leak are already becoming clear.
The likely origin point of the leaked documents appears to be a member of the Massachusetts Air National Guard, Jack Teixeira. While the precise motivation remains under investigation, the documents, spanning a wide range of intelligence assessments and operational plans, were likely accessed through Teixeira’s authorized access to classified information. This highlights the inherent vulnerabilities within even the most secure systems – human error and negligence remain significant factors in compromising sensitive data.
Dissemination Methods Within the Discord Server
The leaked documents were shared within a small, private Discord server, a platform known for its popularity among gamers and online communities. Teixeira allegedly shared the documents over an extended period, fostering a sense of community and trust among a select group of users. The method of sharing likely involved direct messaging, potentially utilizing the server’s file-sharing capabilities. The informal and often casual nature of online communication on such platforms contributed to the initial spread, as users readily shared the documents amongst themselves without fully appreciating the implications of their actions. The informal, closed nature of the server initially prevented widespread dissemination, a critical factor in the initial stages of the leak.
The Chain of Events Leading to Public Release
The initial sharing within the Discord server eventually led to the documents being shared beyond the initial group. This expansion likely involved several steps: screenshots taken and circulated outside the group, users leaving the server and taking the information with them, and potentially deliberate attempts to leak the information to broader audiences. The exact sequence remains under investigation, but the leak’s escalation from a small, closed group to the public domain is a critical aspect requiring further analysis. This demonstrates the challenges in containing information once it has been disseminated online, even within a relatively contained environment.
Timeline of the Leak
While precise dates are still emerging from investigations, a rough timeline can be constructed. The initial sharing of the documents within the Discord server likely began several months prior to their public exposure. The period of internal circulation within the closed server may have lasted for weeks or even months, allowing the information to spread among a small, tightly knit group. The leak to the wider public likely occurred in early 2023, followed quickly by widespread media coverage within days. This rapid escalation underscores the speed at which sensitive information can spread online and the challenges faced by authorities in controlling its dissemination. The timing of the leak and the subsequent media frenzy highlighted the vulnerability of classified information in the digital age and the need for stronger security protocols.
Content of the Leaked Documents and their Implications
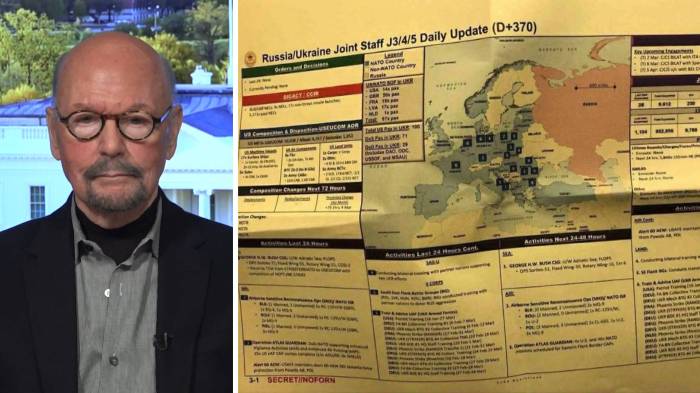
The leaked Pentagon documents, circulating widely online, offer a glimpse into the US intelligence community’s assessment of the war in Ukraine and its broader geopolitical implications. The sheer volume of information, ranging from battlefield assessments to internal memos, presents a complex picture, challenging existing narratives and raising significant questions about the war’s trajectory and the effectiveness of Western support. This detailed analysis focuses on the key revelations and their potential consequences.
The leaked documents paint a nuanced picture of the Ukrainian military’s capabilities and the progress of the conflict. They detail assessments of Ukrainian ammunition stockpiles, troop deployments, and battlefield losses, providing insights into the operational realities on the ground. These assessments, while not necessarily painting a uniformly bleak picture, do reveal challenges faced by the Ukrainian forces, including potential shortages of certain crucial munitions and the ongoing struggle to maintain offensive momentum. The documents also reveal internal debates and differing perspectives within the US intelligence community itself, highlighting the complexities of interpreting intelligence data and predicting the future course of the war.
Ukrainian Military Capabilities and Battlefield Assessments
The documents contain detailed assessments of the Ukrainian military’s capabilities and the effectiveness of Western military aid. Specifically, they offer granular insights into the consumption rate of ammunition, highlighting potential supply chain vulnerabilities. For example, leaked intelligence may detail the depletion of specific types of artillery shells, indicating potential future limitations on offensive operations. This information, while sensitive, provides a crucial understanding of the logistical challenges facing Ukraine and the necessity for continued and potentially increased Western support. The documents also assess the effectiveness of various weapon systems provided by Western allies, offering valuable feedback for future aid packages. This level of detail, while potentially damaging, could ultimately lead to a more effective and tailored approach to supporting the Ukrainian war effort.
Impact on the Ongoing War in Ukraine, Leaked pentagon documents ukraine discord
The leak’s impact on the ongoing war is multifaceted. The revelation of sensitive intelligence could potentially embolden Russia, offering insights into Ukrainian strategies and vulnerabilities. Conversely, it could also prompt Ukraine to adjust its tactics and improve its operational security. The information could also influence the morale of both sides, depending on how the information is interpreted and disseminated. The leak’s overall impact remains uncertain, as the extent to which the information is accurate and actionable remains to be fully determined. For example, if Russia uses the leaked intelligence to anticipate and counter Ukrainian offensives, it could significantly alter the course of the conflict.
Implications for US Foreign Policy and Relations with Allies
The leak has severely damaged US credibility and trust amongst its allies. The disclosure of sensitive intelligence undermines confidence in US intelligence gathering and sharing practices. Allies may be hesitant to share intelligence with the US in the future, fearing similar leaks. This could significantly hamper future collaborative efforts and intelligence sharing initiatives, potentially weakening the effectiveness of Western alliances. The damage to trust extends beyond intelligence sharing; it impacts overall diplomatic relations and strategic partnerships, raising questions about the reliability of the US as a security partner. The consequences for US foreign policy could be long-lasting and far-reaching.
Comparison with Publicly Available Intelligence
While some information in the leaked documents aligns with publicly available intelligence, other details represent new and previously undisclosed insights. Publicly available intelligence often provides a broader, more generalized picture, while the leaked documents offer a much more granular and specific view of the situation on the ground. For instance, while publicly available intelligence may indicate a general shortage of ammunition, the leaked documents might specify the exact types and quantities of ammunition in short supply. This level of detail underscores the potential sensitivity of the leaked information and the potential damage it could cause. The comparison between the leaked and public information highlights the limitations of open-source intelligence and the value – and vulnerability – of classified intelligence.
The Role of the Discord Server and its Members

Source: nyt.com
The leaked Pentagon documents detailing the Ukraine conflict are raising serious questions about intelligence sharing. It’s a messy situation, mirroring the complexities of another kind of tangled mess: the global challenge of polyester recycling , which requires innovative solutions to untangle its environmental impact. Ultimately, both scenarios demand transparency and effective strategies for a better future.
The leaked Pentagon documents weren’t just casually tossed onto the internet; they found their way into a specific online community: a Discord server, a platform primarily known for gamers and online communities. Understanding this server’s nature, its members’ motivations, and the subsequent online reaction is crucial to grasping the full scope of this security breach.
The Discord server in question, while initially seemingly innocuous, acted as a hub for individuals interested in military matters and strategy. It wasn’t a clandestine group operating in the shadows; rather, it was a space where users, some with apparent military backgrounds, engaged in discussions, shared information, and, in this instance, facilitated the dissemination of highly classified documents. The server’s relatively open nature, while not explicitly designed for espionage, inadvertently became a conduit for the leak.
The Motivations and Backgrounds of Involved Individuals
The individuals involved in sharing and discussing the leaked documents represented a diverse range of backgrounds and motivations. Some appear to have been driven by a desire to share information, perhaps believing it to be in the public interest or to challenge established narratives. Others may have been motivated by a sense of camaraderie within the online community, a desire for recognition, or even malicious intent. A thorough investigation is needed to fully understand the complex web of motivations driving each individual’s actions. The age range spanned from teenagers to adults, highlighting the accessibility of sensitive information within seemingly casual online spaces. It’s important to note that not all members of the server were involved in the sharing or discussion of classified material; many were simply participants in the server’s general discussions.
The Online Community’s Reaction to the Leaked Information
The initial reaction within the Discord server was a mixture of shock, disbelief, and excitement. The gravity of the situation likely didn’t fully register for some users immediately. However, as the scale of the leak became apparent, the tone shifted to concern and apprehension. Outside the server, the reaction was varied. Some celebrated the release of the information, viewing it as a form of transparency and accountability. Others condemned the leak, emphasizing the severe security risks and potential harm to national security. The broader online conversation mirrored this division, with intense debate regarding the ethics of releasing classified information and the potential consequences. The leak also sparked conversations about the accessibility of sensitive information and the need for improved security measures in both government and online communities.
Security Measures (or Lack Thereof) within the Discord Server
The incident highlights significant vulnerabilities in online security, particularly within seemingly casual online communities. The server’s lack of robust security measures, coupled with the potentially naive approach to handling sensitive information by some members, allowed for the rapid and widespread dissemination of the classified documents. This incident underscores the need for increased awareness regarding online security and the potential risks associated with sharing information online, even within seemingly closed communities. The ease with which the documents were shared and spread points to a lack of stringent access controls and verification processes within the server, as well as a potential lack of understanding amongst some users about the gravity of handling classified material. This case serves as a stark reminder of the need for comprehensive security protocols and user education in online environments where sensitive information might be discussed.
Legal and Security Ramifications

Source: themoscowtimes.com
The Pentagon leak, involving highly sensitive military intelligence documents shared on a Discord server, carries significant legal and security ramifications for all involved. The potential penalties are severe, extending beyond the immediate individuals responsible to encompass systemic failures within the US Department of Defense and potentially impacting national security. Understanding these ramifications is crucial for preventing future incidents.
Potential Legal Consequences for Involved Individuals
The individuals involved in the leak and distribution face a range of potential charges under both federal and military law. These could include violations of the Espionage Act of 1917, which prohibits unauthorized disclosure of national defense information, carrying penalties of up to life imprisonment. Additional charges might include theft of government property, unauthorized access to classified information, and conspiracy. The severity of the charges will depend on the individual’s role in the leak, their level of access to classified information, and the potential damage caused by the disclosure. The prosecution will likely focus on demonstrating intent and the harm caused by the leaked information. For example, if an individual knowingly leaked information that compromised ongoing military operations or endangered human lives, they would face far more serious consequences than someone who passively shared the information without understanding its significance.
Security Breaches Enabling the Leak
The leak highlights significant security vulnerabilities within the US military’s handling of classified information. The initial breach likely involved unauthorized access to a computer system containing classified documents, possibly through weak passwords, phishing attacks, or insider threats. The subsequent spread through a Discord server demonstrates a failure to monitor and control the flow of information, even outside of official channels. The ease with which the documents were disseminated underscores a need for stricter access controls, improved cybersecurity protocols, and enhanced training for personnel handling classified materials. A lack of robust monitoring systems, particularly on social media and online forums, allowed the leak to spread rapidly and widely before being detected. The case emphasizes the need for more sophisticated detection mechanisms and proactive threat intelligence gathering.
Examples of Similar Past Leaks and Their Consequences
Numerous past leaks of classified information have resulted in significant consequences. The WikiLeaks disclosures of classified US military documents and diplomatic cables, for example, exposed sensitive information and damaged international relations. Edward Snowden’s leak of NSA surveillance programs sparked widespread debate about government surveillance and privacy rights, leading to legal battles and international repercussions. These cases demonstrate the far-reaching consequences of unauthorized disclosures, including damage to national security, erosion of public trust, and legal repercussions for those involved. Each case served as a cautionary tale, yet the Pentagon leak demonstrates that similar vulnerabilities persist.
Hypothetical Strategy to Prevent Future Leaks
Preventing future leaks requires a multi-pronged approach addressing both technical and human factors. This involves strengthening cybersecurity measures, improving personnel training, and enhancing oversight of information sharing.
| Measure | Feasibility | Drawbacks |
|---|---|---|
| Enhanced cybersecurity training for all personnel with access to classified information. | High | Requires significant time and resource investment. |
| Implementation of more robust access control systems, including multi-factor authentication and stricter password policies. | Medium | May cause some inconvenience for users and require system upgrades. |
| Regular security audits and penetration testing to identify and address vulnerabilities. | Medium | Can be costly and time-consuming. |
| Improved monitoring of social media and online forums for leaks of classified information. | Low | Difficult to monitor all platforms and identify leaked information effectively. |
| Stricter enforcement of regulations regarding the handling and dissemination of classified information. | High | May stifle legitimate information sharing and collaboration. |
The Impact on Public Perception and Trust: Leaked Pentagon Documents Ukraine Discord
The leak of classified Pentagon documents regarding the Ukraine war has sent shockwaves through the public sphere, significantly impacting trust in the US government and its intelligence agencies. The sheer volume of sensitive information revealed, coupled with the seemingly casual manner of its dissemination, has fueled widespread skepticism and eroded confidence in the government’s ability to protect national security secrets. This erosion of trust extends beyond the government itself, casting doubt on the reliability of official narratives surrounding the conflict in Ukraine.
The leak’s effect on public perception of the war in Ukraine is multifaceted. For some, the documents confirm existing suspicions about the conflict’s complexities and the limitations of official reporting. Others, however, might feel disillusioned or even manipulated, questioning the integrity of the information they have been receiving from both government and media sources. The revelation of intelligence assessments and internal deliberations raises questions about the transparency and accuracy of official communication surrounding the war. The uncertainty created by this information gap can lead to increased public anxiety and polarization.
Comparison with Past Leaks
This incident echoes previous high-profile leaks, such as the WikiLeaks disclosures and the Edward Snowden revelations. However, the context and nature of this leak differ significantly. While past leaks often focused on broader issues of government surveillance or foreign policy, this leak directly impacts an ongoing military conflict, with potentially immediate and severe consequences for national security and international relations. The speed and reach of the information’s dissemination through social media also marks a notable difference from previous events, amplifying the impact and potentially hindering government efforts to control the narrative. The public response to this leak, therefore, shares similarities with past reactions to large-scale information breaches, but the specific implications and ramifications are unique to this situation. For instance, while past leaks might have sparked debates about privacy rights, this leak focuses public attention on the accuracy and reliability of intelligence assessments during a time of war.
Public, Media, and Government Reactions
The leak has generated a wide range of reactions. Understanding these diverse perspectives is crucial to grasping the full impact of this event.
- Perspective 1: Erosion of Trust in Government and Intelligence Agencies. Many citizens express concerns about the government’s ability to safeguard classified information and maintain the integrity of its intelligence operations. This fuels cynicism and skepticism toward official statements and narratives.
- Perspective 2: Increased Scrutiny of US Involvement in Ukraine. The leak has prompted renewed debate about the extent and nature of US involvement in the Ukraine conflict. Some question the wisdom of US support, while others reaffirm their commitment to aiding Ukraine against Russian aggression. This perspective highlights the ongoing polarization surrounding the war itself.
- Perspective 3: Concerns about National Security Risks. Government officials and security experts are primarily concerned about the potential damage to national security stemming from the disclosure of sensitive intelligence. This concern focuses on the risks of compromised operations, potential harm to intelligence sources, and the erosion of trust among allies.
- Perspective 4: Media’s Role in Disseminating and Analyzing Information. The media plays a pivotal role in informing the public about the leak and its implications. Some outlets focus on the national security risks, while others highlight the broader political and ethical implications. The varied approaches adopted by different news organizations reflect the diverse perspectives within the public sphere.
Visual Representation of Information Flow
Source: democracynow.org
Understanding the spread of the leaked Pentagon documents requires visualizing the complex web of actors and platforms involved. A clear diagram is crucial for comprehending the speed and reach of the leak, highlighting the key stages from the initial breach to widespread dissemination across the internet.
The flow of information can be depicted as a branching network. The initial source, likely a single individual within a secure network, would be represented as a central node. From this node, lines would radiate outwards, representing the initial transfer of the documents. These lines would lead to subsequent nodes representing intermediary individuals or groups, perhaps within the Discord server or other online communities. Each subsequent transfer would be represented by further branching lines, illustrating the exponential growth of dissemination. Different line thicknesses could reflect the volume of data shared at each stage, with thicker lines indicating larger data transfers. The nodes themselves could be color-coded to indicate the actors involved—e.g., government officials (red), military personnel (green), civilians (blue), and members of online communities (yellow). Finally, the network would end with numerous terminal nodes representing various online platforms, news outlets, and social media channels where the documents ultimately surfaced. This visual representation would effectively showcase the chain of events, highlighting the role of each actor and the escalating impact of the leak.
Diagram of Information Flow
Imagine a diagram resembling a tree, starting with a single, dark red node labeled “Initial Leak Source” at the top. From this node, several thinner, dark blue lines branch out, leading to smaller, light blue nodes representing individuals within the initial Discord server. These nodes are connected by even thinner lines to other light blue nodes representing further dissemination within the server. Then, thicker, dark green lines emanate from these nodes, reaching larger, dark green nodes representing various online platforms like Twitter, Telegram, and potentially news websites. The size of the dark green nodes would be proportional to the amount of exposure on each platform. Finally, from these larger nodes, numerous thin, light gray lines extend outwards, representing the countless individual users who accessed and shared the documents. The entire network visually represents the cascading effect of the leak, emphasizing the rapid and expansive spread of the information.
Visual Representation of Online Platform Spread
A concentric circle diagram would effectively illustrate the spread of the leaked information across different online platforms. The innermost circle represents the initial Discord server, depicted in a dark shade of blue, symbolizing the origin point. The subsequent concentric circles would represent different online platforms, expanding outwards to show the increasing reach of the leak. Each circle could be color-coded to represent a specific platform—for example, Twitter in light blue, Telegram in purple, and news websites in green. The thickness of each circle could correspond to the volume of leaked information shared on that particular platform. Smaller icons within each circle could represent individual users or groups actively engaging with and sharing the leaked content. This visual representation would clearly demonstrate the concentric spread of the information from a singular point of origin to a wider online audience.
Final Summary
The leaked Pentagon documents saga serves as a stark reminder of the vulnerabilities inherent in even the most secure systems and the far-reaching consequences of unchecked information dissemination. The incident underscores the urgent need for improved security protocols and a deeper understanding of the complexities of online communities and their potential to amplify sensitive information globally. The ongoing investigation and its ultimate conclusions will undoubtedly shape future approaches to information security and international relations, leaving an indelible mark on the digital landscape and the global stage.
