Internet connection records UK surveillance: It’s a topic that sparks debate, raising questions about privacy versus national security. The UK’s approach to data retention and access by law enforcement and intelligence agencies is complex, balancing the need to investigate crime and terrorism with the fundamental right to privacy. This exploration delves into the legal framework, data retention policies, surveillance techniques, and the impact on civil liberties, examining both the potential benefits and significant risks involved.
From the legal basis for accessing internet connection records to the technological capabilities employed, we’ll uncover the realities of this digital oversight. We’ll analyze the effectiveness of different surveillance techniques, weighing their impact on individual privacy against their potential contribution to national security. We’ll also explore the ongoing public debate, examining the arguments from various stakeholders and exploring potential policy reforms.
Legal Framework of Internet Connection Records in the UK
The UK’s legal framework surrounding the retention and access of internet connection records is a complex interplay of legislation, judicial interpretation, and ongoing debate. It balances national security concerns with the fundamental right to privacy, a delicate balance constantly under scrutiny. This framework is primarily shaped by the Investigatory Powers Act 2016 (IPA), but also draws upon other relevant legislation and case law.
The Investigatory Powers Act 2016 (IPA) is the cornerstone of the UK’s legal framework governing the acquisition and use of internet connection records. This Act sets out the powers of law enforcement and intelligence agencies to obtain such data, specifying the types of records that can be accessed (like IP addresses, timestamps, and location data) and the conditions under which such access is permitted. The IPA aims to provide a legal framework that is both effective in tackling crime and terrorism while respecting individual rights. However, its effectiveness and proportionality remain subjects of ongoing discussion and legal challenges.
The Legal Processes for Accessing Internet Connection Records
The IPA establishes a rigorous process for obtaining warrants or authorizations to access internet connection records. This typically involves applications made to a designated judge or magistrate who assesses the necessity and proportionality of the request, considering the potential impact on individual privacy. The application must demonstrate a clear legal basis for the request, such as suspicion of a serious crime, and must specify the precise information sought. The judge then weighs the public interest in investigating the crime against the individual’s right to privacy before issuing a warrant. Strict limitations and oversight mechanisms are intended to prevent abuse of these powers. For instance, warrants are usually time-limited and subject to judicial review.
Comparison with Other European Countries
The UK’s approach to internet connection record retention differs significantly from other European countries. While many EU member states have data retention laws, the specifics vary considerably. Some countries have stricter requirements regarding the duration of retention and the types of data collected, while others have a more permissive approach. The European Court of Human Rights has played a significant role in shaping data retention laws across Europe, emphasizing the need for proportionality and legal safeguards. The UK’s system, particularly as defined by the IPA, has been subject to scrutiny in this context, with some critics arguing that it does not adequately balance security concerns with individual rights compared to other European jurisdictions. A detailed comparative analysis would require a dedicated study, as individual country laws and their application are extremely nuanced.
Rights and Protections Afforded to Individuals
Individuals whose internet connection records are accessed are afforded certain rights and protections under UK law. These include the right to be informed (where legally permissible), the right to challenge the legality of the access in court, and the right to seek redress for any misuse of their data. The IPA Artikels specific procedures for informing individuals about access to their data, although there are exceptions for national security reasons. The independent Investigatory Powers Tribunal provides a mechanism for individuals to challenge the legality of surveillance activities, including the access to their internet connection records. Furthermore, data protection legislation, such as the UK GDPR, provides additional safeguards against unlawful processing of personal data. However, the balance between national security and individual rights continues to be a subject of debate and ongoing legal challenges.
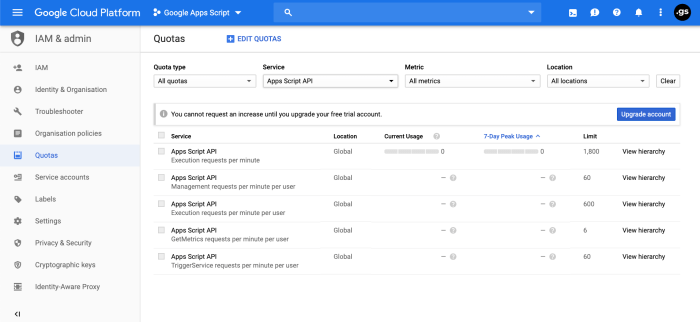
Data Retention Policies and Practices
Source: sstatic.net
Big Brother’s watching, they say, with UK internet connection records under constant scrutiny. But even the digital gaze might pale in comparison to the sheer scale of another pervasive problem: the mountain of plastic waste. Check out this article on innovative solutions like plastic pollution packaging notpla for a glimpse of hope. Meanwhile, back to the internet, the question remains: what are they really tracking?
The UK’s legal framework surrounding internet connection records necessitates a clear understanding of how ISPs handle the data they collect. This involves examining the types of data retained, the duration of storage, the security measures employed, and the inherent vulnerabilities of the system. The balance between national security and individual privacy is a constant point of contention in this area.
Internet Service Providers (ISPs) in the UK retain various types of internet connection records, all contributing to a comprehensive picture of user online activity. The exact nature of this data varies between providers, but generally includes information crucial for billing, network management, and potentially, law enforcement investigations. Understanding the specific data points, and their retention periods, is crucial for assessing both the potential benefits and risks of this data collection.
Types of Retained Internet Connection Records
ISPs typically retain a range of data, including but not limited to: IP addresses (both source and destination), timestamps indicating connection start and end times, and the volume of data transmitted. Some ISPs may also log URLs visited, although this is generally more sensitive and subject to stricter retention policies. Precisely what data is retained often depends on the ISP’s internal policies, the technical capabilities of their systems, and legal requirements. For example, some providers might log detailed information about specific applications used, while others might focus on a more aggregated view of internet usage. The lack of complete standardization across ISPs presents a challenge for comprehensive oversight and analysis.
Typical Retention Periods for Internet Connection Records
Retention periods vary significantly depending on the type of data and the ISP’s internal policies. Basic connection records, like IP addresses and timestamps, are often retained for a period of six to twelve months for billing and network management purposes. However, more detailed records, such as those relating to specific websites visited or applications used, may be kept for shorter durations or not retained at all, due to privacy concerns and data storage limitations. Legal requirements can also influence retention periods, with some data potentially being held for longer if required for ongoing investigations. This lack of consistency highlights the need for clearer, more standardized regulations governing data retention across all ISPs.
Security Measures Implemented by ISPs
ISPs employ a variety of security measures to protect the confidentiality and integrity of internet connection records. These measures typically include data encryption both in transit and at rest, access control mechanisms to limit access to authorized personnel only, and regular security audits to identify and address vulnerabilities. However, the effectiveness of these measures varies greatly depending on the resources and expertise of individual ISPs. Furthermore, the sheer volume of data involved, combined with the constantly evolving threat landscape, presents a continuous challenge for maintaining robust security. Examples of security measures might include multi-factor authentication for accessing data stores, regular penetration testing to identify weaknesses, and employing intrusion detection systems to monitor for malicious activity.
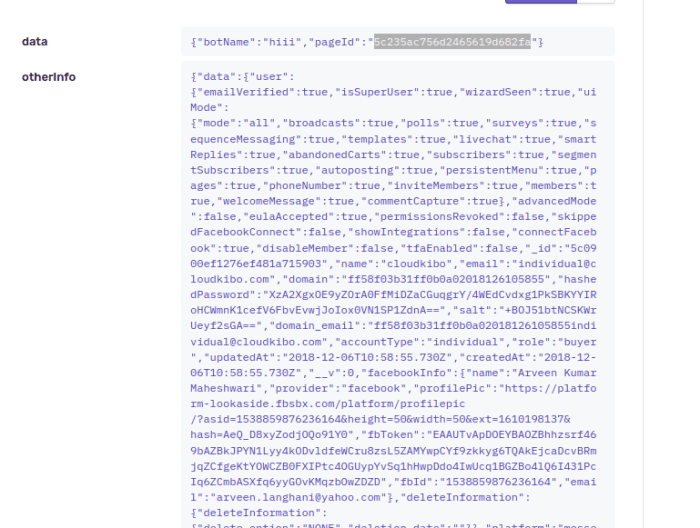
Potential Vulnerabilities and Risks Associated with Internet Connection Records
Despite security measures, the storage and handling of internet connection records present several significant vulnerabilities and risks. Data breaches, whether through hacking or insider threats, pose a considerable risk, potentially exposing sensitive user information. Furthermore, the potential for misuse of this data by unauthorized individuals or entities, including for surveillance or identity theft, is a serious concern. The sheer scale of the data collected also presents logistical challenges in ensuring its secure storage and management. For example, a large-scale data breach could expose the browsing history and online activities of millions of users, leading to significant privacy violations and potential harm. Similarly, unauthorized access to this data by law enforcement or intelligence agencies without proper oversight could lead to abuses of power and infringements on civil liberties.
Surveillance Capabilities and Techniques
The UK’s extensive network of internet connection records provides law enforcement and intelligence agencies with significant capabilities for surveillance. Access to these records, coupled with sophisticated analytical techniques, allows for the tracking of individuals’ online activities, identifying potential suspects, and building investigative leads. However, this power comes with significant ethical and privacy implications that demand careful consideration.
The capabilities of law enforcement and intelligence agencies to access and analyze internet connection records are substantial. They can obtain data on the websites visited, the duration of visits, the IP addresses used, and communication metadata, such as the time and duration of calls or messages. This data can be used to reconstruct an individual’s online behaviour, identify associates, and map communication networks. The scale of data collected allows for the identification of patterns and trends that might otherwise go unnoticed.
Data Extraction and Analysis Techniques
Law enforcement and intelligence agencies employ a range of technologies and techniques to extract information from internet connection records. These include automated data mining tools capable of sifting through massive datasets to identify specific patterns or s, sophisticated network analysis techniques to map relationships between individuals and organizations, and specialized software designed to correlate data from various sources, such as internet connection records, call detail records, and financial transactions. The analysis often involves complex algorithms and statistical modeling to identify anomalies and potential threats.
Effectiveness Across Different Investigations
The effectiveness of using internet connection records varies significantly depending on the nature of the investigation. In cases involving cybercrime, such as online fraud or hacking, these records can provide crucial evidence, identifying perpetrators and tracing their activities. Similarly, in terrorism investigations, they can help track communication networks and identify potential threats. However, in less technologically focused crimes, their value might be more limited. For instance, while internet connection records might provide circumstantial evidence in a murder investigation, they are unlikely to be the primary source of evidence.
Ethical Considerations
The use of internet connection records for surveillance raises significant ethical considerations. The potential for mass surveillance and the erosion of privacy are major concerns. The lack of transparency around data collection and analysis practices, coupled with the potential for misuse or abuse of power, further exacerbates these concerns. Striking a balance between national security and individual liberties is a complex challenge that requires careful consideration of the legal framework, oversight mechanisms, and ethical guidelines governing the use of this powerful surveillance tool.
Comparison of Surveillance Techniques
| Technique | Effectiveness | Privacy Risk | Example |
|---|---|---|---|
| Data Mining | High for identifying patterns and trends; variable for specific individuals. | High; potential for mass surveillance and profiling. | Identifying individuals involved in a coordinated online fraud scheme through analysis of IP addresses and website visits. |
| Network Analysis | High for mapping relationships and communication networks. | High; reveals sensitive connections between individuals. | Mapping communication networks between suspected terrorists based on their online interactions. |
| Correlation with other data sources | Variable; depends on the availability and quality of other data. | High; combining data from multiple sources increases the risk of privacy violation. | Combining internet connection records with financial transaction data to identify individuals involved in money laundering. |
| Search | Low unless specific s are known; potential for false positives. | Moderate; limited to specific searches but can still reveal sensitive information. | Searching for specific terms related to bomb-making techniques in internet connection records. |
Impact on Privacy and Civil Liberties: Internet Connection Records Uk Surveillance
The widespread availability of internet connection records (ICRs) in the UK presents a significant challenge to individual privacy and fundamental civil liberties. The sheer volume of data collected – encompassing websites visited, apps used, and communication patterns – creates a detailed profile of an individual’s online life, potentially revealing sensitive information about their beliefs, associations, and activities. This raises serious concerns about the potential for misuse and abuse of this powerful surveillance tool.
The potential for chilling effects on freedom of expression and association is substantial. Individuals may self-censor their online activities if they fear that their communications or online engagement could be monitored and used against them. This self-censorship could stifle dissent, limit the free exchange of ideas, and hinder the ability of individuals and groups to organize and advocate for their interests. The very act of knowing that one’s online activity is being recorded can create a chilling effect, leading to a less vibrant and open online environment.
Impact on Individual Privacy
Access to ICRs allows authorities and potentially private entities to reconstruct a detailed picture of an individual’s online behaviour. This includes not only the websites visited but also the duration of visits, the specific pages accessed, and the timing of online activities. This level of granularity can reveal intimate details about an individual’s personal life, political affiliations, health concerns, and relationships, all without their explicit consent. The potential for this data to be misused, either intentionally or unintentionally, is significant. For instance, employers could access ICRs to monitor employee activities outside of work hours, while marketers could use the data to create highly targeted and potentially intrusive advertising campaigns. The cumulative effect of this constant surveillance can lead to a feeling of being constantly monitored and a reduction in personal autonomy.
Implications for Freedom of Expression and Association
The availability of ICRs can significantly impact freedom of expression and association. Individuals involved in political activism, journalism, or advocacy for marginalized groups may be particularly vulnerable to surveillance and potential reprisal. Knowing that their online communications are being monitored could lead to self-censorship, preventing them from expressing their views freely or associating with like-minded individuals. This chilling effect can undermine democratic processes and limit the ability of citizens to hold power accountable. For example, journalists investigating sensitive topics may be reluctant to communicate with sources online for fear of compromising their anonymity and safety. Similarly, individuals participating in online forums discussing controversial political issues may be less likely to express their opinions openly if they believe their communications are being monitored.
Cases Raising Human Rights Concerns
While specific cases involving the misuse of ICRs in the UK might not be publicly available due to legal restrictions or ongoing investigations, numerous examples from other countries illustrate the potential for human rights abuses. In several instances, access to ICRs has been used to target journalists, activists, and political dissidents. The lack of transparency and robust oversight mechanisms surrounding the collection and use of ICRs further exacerbates these concerns. The potential for mass surveillance, disproportionate targeting of specific groups, and the erosion of due process are all serious human rights implications. The lack of easily accessible legal recourse for individuals whose privacy has been violated further compounds the issue.
Hypothetical Scenario of Misuse
Let’s imagine a scenario involving a university student, Sarah, who is actively involved in environmental activism.
- Event 1: Sarah participates in online forums and social media groups dedicated to climate change activism, sharing her views and organizing protests.
- Event 2: Law enforcement agencies, without a warrant or proper justification, access Sarah’s ICRs, revealing her online activities and associations.
- Event 3: This information is used to identify Sarah and her fellow activists, leading to increased surveillance and potential intimidation.
- Event 4: Sarah faces increased scrutiny from her university, potentially impacting her academic standing or leading to disciplinary action.
- Event 5: Sarah’s employer, accessing her ICRs through a data broker, terminates her employment based on her political affiliations revealed through her online activity.
This scenario demonstrates how seemingly innocuous online activities can be weaponized against individuals, leading to significant consequences for their freedom of expression, association, and employment. The lack of transparency and accountability surrounding the use of ICRs exacerbates the potential for such abuses.
Public Debate and Policy Recommendations
Source: githubusercontent.com
The ongoing debate surrounding internet connection record (ICR) surveillance in the UK is a complex interplay of national security concerns, individual privacy rights, and the practical challenges of data handling. It highlights the tension between protecting citizens from terrorism and crime, and safeguarding their fundamental freedoms in the digital age. This necessitates a careful consideration of various perspectives and a nuanced approach to policy reform.
The core arguments revolve around the balance between the state’s need for intelligence gathering to prevent crime and terrorism, and the potential for mass surveillance to infringe on individual privacy and civil liberties. Opponents argue that ICR surveillance is overly broad, disproportionate, and lacks sufficient safeguards against misuse. Proponents, on the other hand, emphasize the crucial role of ICR data in solving serious crimes and preventing terrorist attacks, highlighting the potential for missed opportunities to prevent harm if such data were unavailable.
Key Stakeholders in the Debate
The debate involves several key stakeholders, each with their own vested interests and perspectives. The UK government champions the use of ICRs for national security, often emphasizing its importance in counter-terrorism efforts. Internet Service Providers (ISPs) are crucial players, as they are responsible for collecting and retaining the data. Their involvement raises concerns about data security, potential for misuse, and the financial burden of compliance. Civil liberties groups, such as Liberty and Privacy International, actively campaign against ICR surveillance, highlighting its potential for abuse and the erosion of fundamental rights. Additionally, legal professionals and academics contribute to the debate by analyzing the legal framework, offering critical assessments of the surveillance practices, and proposing alternative solutions.
Proposals for Reforming Data Protection Laws
Several proposals aim to reform or strengthen data protection laws related to ICRs. These include strengthening the legal basis for data retention, implementing stricter data minimization principles, establishing independent oversight mechanisms to scrutinize the use of ICRs, and enhancing transparency regarding the scope and extent of surveillance. Proposals for stronger judicial oversight of warrants and increased scrutiny of government requests for data are also common. There’s also ongoing debate about the duration of data retention, with calls to reduce the current retention period, citing the potential for prolonged surveillance and the risks associated with storing large amounts of sensitive data.
Impact of Policy Options on National Security and Privacy
Different policy options will inevitably affect the balance between national security and individual privacy. For instance, stricter data minimization policies, limiting the types of data collected and retained, would enhance privacy but might reduce the effectiveness of law enforcement investigations. Conversely, extending data retention periods could improve the ability to solve complex crimes, but at the cost of increased surveillance and potential for abuse.
- Policy Recommendation 1: Stricter Data Minimization: Effect on Privacy: Significantly improved. Effect on National Security: Potentially reduced effectiveness of investigations, particularly in complex cases requiring long-term analysis.
- Policy Recommendation 2: Independent Oversight Body: Effect on Privacy: Enhanced through increased accountability and transparency. Effect on National Security: Minimal impact, potentially improved through more targeted and effective surveillance.
- Policy Recommendation 3: Shorter Data Retention Period: Effect on Privacy: Improved, reducing the period of potential surveillance. Effect on National Security: Potentially reduced ability to investigate crimes with longer timelines.
- Policy Recommendation 4: Strengthened Judicial Oversight: Effect on Privacy: Improved through increased judicial scrutiny of surveillance requests. Effect on National Security: Minimal impact, potentially improved through more targeted and legally sound surveillance practices.
Technological Countermeasures and Mitigation Strategies
Protecting your online privacy in the face of potential surveillance of internet connection records requires a proactive approach. While complete anonymity is virtually impossible, employing various technological measures can significantly reduce your digital footprint and hinder the ability of surveillance systems to track your online activities. This involves understanding both the strengths and limitations of available tools and adopting a layered security strategy.
The digital landscape is constantly evolving, and so too are the methods used to monitor online activity. This means that reliance on a single solution is risky; a multi-faceted approach offers the best protection. It’s crucial to remember that no single technology offers foolproof protection, and even the most robust methods can be circumvented with sufficient resources and determination.
Virtual Private Networks (VPNs) and Encryption
VPNs mask your IP address, encrypting your internet traffic and routing it through a secure server in a different location. This makes it significantly harder to trace your online activities back to you. Encryption, both at the network level (like with a VPN) and at the application level (such as using HTTPS websites), further protects your data from prying eyes. However, VPNs are not a silver bullet. Some VPN providers may log user data, potentially undermining their privacy benefits. Furthermore, governments can still obtain data from VPN providers through legal processes, or through sophisticated methods that bypass VPN encryption in certain cases. The effectiveness of a VPN also depends on its security protocols and the trustworthiness of the provider. Choosing a reputable VPN with a strong no-logs policy is crucial.
Limitations of Technological Measures, Internet connection records uk surveillance
While technologies like VPNs and encryption offer valuable protection, they are not infallible. Sophisticated surveillance systems can employ techniques such as deep packet inspection to analyze encrypted traffic for patterns, even if they cannot decipher the content. Moreover, metadata—data about your online activity, such as the websites you visit and the duration of your sessions—can still be collected even when using encryption. This metadata, while not revealing the content of your communications, can still reveal a significant amount about your behaviour and associations. Furthermore, the effectiveness of these measures is dependent on the user’s technical knowledge and diligence in maintaining their security practices.
Challenges in Implementing Robust Technological Safeguards
Implementing robust technological safeguards against mass surveillance faces numerous challenges. These include the constant evolution of surveillance techniques, the complexity of modern internet infrastructure, and the inherent difficulty of balancing security with usability and accessibility. There’s also the problem of the “security arms race”—as new security measures are developed, surveillance technologies evolve to circumvent them, leading to an ongoing cycle of technological innovation on both sides. Furthermore, the cost of implementing and maintaining robust security measures can be prohibitive for many individuals and organizations.
Practical Steps to Minimize Digital Footprint
Reducing your digital footprint and minimizing the risk of your internet connection records being accessed requires a multi-pronged approach.
Here are some practical steps individuals can take:
- Use a VPN with a strong no-logs policy from a reputable provider.
- Enable two-factor authentication (2FA) wherever possible.
- Use strong, unique passwords for all online accounts and consider a password manager.
- Be mindful of the data you share online and avoid using public Wi-Fi for sensitive activities.
- Regularly update your software and operating systems to patch security vulnerabilities.
- Use privacy-focused search engines and browsers.
- Review and adjust your privacy settings on social media and other online platforms.
- Consider using encrypted messaging apps for private communications.
- Use Tor Browser for enhanced anonymity when accessing sensitive websites.
- Regularly audit your online accounts and delete unnecessary data.
Final Thoughts
Source: githubassets.com
The UK’s approach to internet connection record surveillance presents a delicate balancing act. While the ability to access this data can be crucial for investigations, the potential for misuse and the impact on individual privacy cannot be ignored. Understanding the legal framework, data retention practices, and surveillance techniques is essential for informed public discourse and the development of policies that effectively protect both national security and fundamental rights. The ongoing debate highlights the need for transparency, robust safeguards, and a continuous reassessment of the balance between security and liberty in the digital age.
