Chatgpt scams apple app store google play – Fake AI apps are flooding the Apple App Store and Google Play, preying on users eager to tap into the latest AI technology. Slick marketing tricks and convincing interfaces mask malicious code designed to steal your data and money. This isn’t just some tech glitch; it’s a full-blown scam targeting unsuspecting users. We’ll dive into the deceptive tactics, the risks involved, and how to protect yourself from becoming the next victim.
From cleverly disguised apps mimicking popular AI tools to sophisticated phishing techniques, scammers are pulling out all the stops. Understanding the methods they use is the first step in avoiding these digital traps. We’ll explore real-world examples of these scams, analyze the technical aspects of these malicious apps, and offer practical advice on how to stay safe in this increasingly complex digital landscape.
Prevalence of Fake Apps
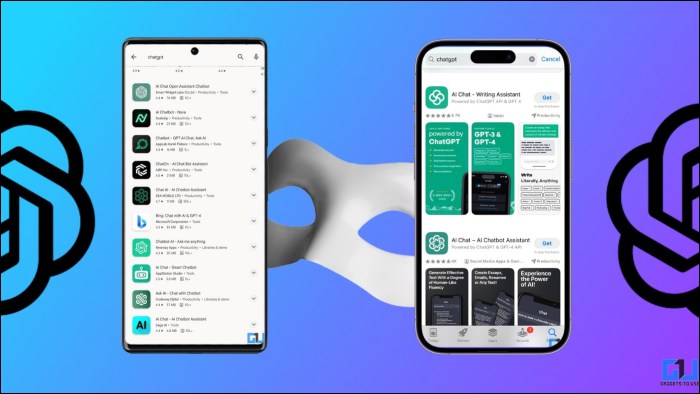
The rise of artificial intelligence has spurred a parallel surge in fraudulent applications masquerading as legitimate AI tools. These fake apps, cleverly designed to mimic the functionality and branding of popular AI services, are proliferating on both the Apple App Store and Google Play, preying on unsuspecting users eager to experience the latest technological advancements. This poses a significant threat, not only financially but also in terms of data security and privacy.
The methods employed by scammers are increasingly sophisticated. They often leverage convincing app icons, descriptions, and screenshots that closely resemble genuine AI applications. Fake reviews, purchased or generated artificially, further bolster their deceptive campaigns. Some even incorporate basic AI functionalities to create a veneer of legitimacy, while secretly harvesting user data or installing malware. The apps may promise advanced features that are unavailable in the legitimate counterparts or offer premium functionalities for a fee, ultimately leading to financial loss for the victims.
Security Measures by Apple and Google
Apple and Google both employ a multi-layered approach to combat fraudulent apps. Apple’s App Store review process involves manual and automated checks for malicious code and deceptive practices. Google Play Store utilizes similar methods, including automated scanning for malware and a system for flagging suspicious apps based on user reports and data analysis. However, the sheer volume of apps submitted and the ever-evolving tactics of scammers make it a constant arms race. While both platforms have improved their security measures over time, the effectiveness remains a challenge, particularly with sophisticated, well-disguised fraudulent apps.
Examples of Fake AI Apps
| App Name (Example) | Deceptive Features | Method of Operation | Impact on Users |
|---|---|---|---|
| AI Photo Enhancer Pro | Promises unrealistic image enhancement; charges high subscription fees; displays fake user testimonials. | Collects user photos and personal data; uses in-app purchases to generate revenue; hides true functionality behind a paywall. | Financial loss; privacy violation; disappointment due to subpar performance. |
| Smart AI Assistant | Mimics a popular AI assistant’s interface and branding; offers advanced features not found in the legitimate app. | Installs malware; subscribes users to unwanted services; redirects users to phishing websites. | Device compromise; financial loss; exposure to phishing attacks. |
| AI Writer Supreme | Claims to generate high-quality written content; offers a free trial that leads to a costly subscription. | Produces low-quality, generic content; charges exorbitant subscription fees; uses aggressive marketing tactics. | Financial loss; dissatisfaction with the quality of the service; frustration with hidden costs. |
Deceptive Marketing Techniques: Chatgpt Scams Apple App Store Google Play
Source: com.au
Fake Kami apps aren’t just poorly coded; they’re masters of deception. Their marketing strategies are designed to exploit our innate trust in technology and our desire for convenience, all while preying on our psychological vulnerabilities. These apps often leverage the hype surrounding AI to create a veneer of legitimacy, masking their fraudulent nature.
These deceptive tactics go beyond simple misrepresentation. They are carefully crafted psychological campaigns aimed at manipulating user behavior and leading them down a path of downloading and, often, paying for useless, and sometimes dangerous, applications. The creators understand the power of association and leverage it to their advantage, creating an illusion of connection with genuine AI technologies.
Exploitation of User Trust and AI Hype
The current excitement surrounding AI, especially large language models like Kami, makes it fertile ground for scammers. Fake apps often use terms like “AI-powered,” “revolutionary,” and “next-generation” to create a sense of cutting-edge technology, even when the app offers little more than basic functionality or is completely non-functional. This capitalizes on the user’s desire to be at the forefront of technological advancements and their inherent trust in the reputation of established brands like OpenAI (the creator of Kami). They prey on the “fear of missing out” (FOMO) to drive downloads. The implication is that if you don’t download this app, you’re missing out on a groundbreaking innovation.
Psychological Principles Behind Deceptive Marketing
The psychology behind these scams is multifaceted. It relies heavily on cognitive biases, such as confirmation bias (users tend to seek out information confirming their pre-existing beliefs) and the bandwagon effect (users are more likely to download an app if they believe others are using it). The use of positive reviews (often fake) further reinforces this effect. Furthermore, the scarcity principle—creating a sense of urgency by implying limited availability or time-sensitive offers—is frequently employed to pressure users into immediate action before they have time to critically assess the app. The use of appealing visuals and promises of quick solutions further plays on our desire for instant gratification.
Examples of Misleading App Descriptions and Screenshots
The following examples illustrate the deceptive marketing techniques employed by these fraudulent apps:
- App Description: “Experience the power of true AI! Kami Pro unlocks unlimited access to the most advanced language model ever created. Download now and revolutionize your productivity!” Reality: The app offers only basic chatbot functionality, often with limited responses and frequent errors.
- App Description: “Official Kami companion app! Get exclusive features and seamless integration with your Kami account.” Reality: The app is completely unrelated to OpenAI’s Kami and attempts to harvest user data.
- Screenshot: A screenshot showcasing a sleek, modern interface with advanced features, such as real-time translation and advanced writing tools. Reality: The actual app interface is clunky, basic, and lacks most of the promised features.
- App Description: “Limited-time offer! Download now and get 50% off our premium Kami subscription!” Reality: The app is free, but the “premium subscription” is a scam designed to extract payment information.
Financial Risks and User Data Breaches
Downloading and using fake AI apps isn’t just a frustrating waste of time; it’s a serious gamble with your financial well-being and personal information. These apps, often masquerading as legitimate AI tools, can lead to significant financial losses and expose you to identity theft and other privacy violations. The consequences can be far-reaching and devastating.
These malicious applications employ various deceptive tactics to lure unsuspecting users. They might promise incredible features, offer seemingly free trials, or use sophisticated marketing campaigns mimicking legitimate AI companies. Once downloaded, however, the true nature of these apps is revealed: they’re designed to steal your money and your data.
Financial Consequences of Fake AI Apps
The financial repercussions of interacting with fraudulent AI apps can range from minor inconveniences to crippling debt. Users might unwittingly subscribe to costly premium services, encounter hidden fees, or experience unauthorized charges on their credit cards. Some apps may even directly steal funds from linked bank accounts. Furthermore, the emotional distress and time spent resolving these issues can also be significant. The cost of restoring credit after identity theft, for example, can be substantial and protracted.
Types of Compromised User Data
Fake AI apps are adept at collecting a wide range of sensitive user data. This typically includes financial information such as credit card numbers, bank account details, and passwords. Beyond financial details, these apps can also harvest personal information like your name, address, phone number, email address, and even biometric data if the app requests access to your device’s camera or microphone. The collected data is often sold on the dark web or used for targeted phishing attacks.
Real-World Cases of Financial Losses and Data Breaches
While specific details of individual cases involving fake AI apps are often not publicly available due to privacy concerns and ongoing investigations, numerous reports highlight the prevalence of such scams. News articles and cybersecurity blogs frequently detail incidents where users have lost thousands of dollars to fake investment apps promising high returns, or experienced identity theft after downloading seemingly harmless AI productivity tools. These cases often involve sophisticated phishing techniques and cleverly disguised malware.
Hypothetical Scenario Illustrating Risks
Imagine Sarah, a busy professional, downloads a “smart assistant” app promising to streamline her daily tasks. The app boasts AI-powered scheduling and email management, and it’s free to download. Initially, the app functions as advertised. However, after a week, Sarah notices unusual charges on her credit card. She discovers that the app has secretly subscribed her to a premium service with recurring monthly fees. Furthermore, the app’s privacy policy, which she skimmed over during installation, grants it broad access to her contacts, emails, and location data. This data is now potentially in the hands of malicious actors, putting Sarah at risk of identity theft and targeted phishing scams. This scenario, while hypothetical, accurately reflects the real dangers posed by fraudulent AI applications.
Technical Analysis of Malicious Apps
Malicious apps, disguised as legitimate ones, employ a range of sophisticated techniques to infiltrate user devices and steal sensitive information. Understanding these technical aspects is crucial for both developers and users to stay ahead of these threats. This section delves into the common technical features found in such apps, comparing them to their legitimate counterparts and highlighting how malicious actors gain unauthorized access.
Common Technical Features of Malicious Apps
Malicious apps often leverage several common techniques to achieve their nefarious goals. These include obfuscation of code to hinder reverse engineering, the use of dynamic code loading to evade detection, and the exploitation of vulnerabilities in the operating system or other applications. They might also employ techniques to hide their network communication, making it difficult to track their activity. For example, a fake banking app might use heavily encrypted communication channels to transfer stolen credentials to a remote server, making it appear as legitimate network traffic. Another example is the use of rootkits to maintain persistence on the device even after the user attempts to uninstall the app.
Comparison of Code Functionalities
Legitimate apps generally follow established coding practices, prioritizing security and user privacy. Their code is typically well-structured, documented, and easy to understand. In contrast, malicious apps often exhibit characteristics like poorly written code, excessive use of obfuscation techniques, and the inclusion of suspicious libraries or functions. A legitimate photo editing app might use standard image processing libraries, while a malicious counterpart could include hidden code that uploads photos to a remote server without user consent. Furthermore, legitimate apps typically have a clear and concise purpose, while malicious apps often have hidden functionalities that are not advertised to the user.
Unauthorized Access Methods
Malicious apps can gain unauthorized access to user devices through various means. One common method is requesting excessive permissions during installation. Another is exploiting vulnerabilities in the operating system or other apps. They might also use social engineering techniques to trick users into granting unnecessary permissions or installing malicious updates. For example, an app requesting access to contacts, location, and microphone might be legitimate, but only if all those permissions are truly necessary for the app’s functionality. A malicious app might use these permissions to steal user data or track their movements without their knowledge.
Permissions Requested by Legitimate and Fraudulent Apps
The permissions requested by an app are a key indicator of its potential malicious nature. A legitimate app will only request permissions absolutely necessary for its functionality. A fraudulent app, on the other hand, may request a broad range of permissions, exceeding what is required for its stated purpose.
| Permission | Legitimate App | Fraudulent App | Explanation |
|---|---|---|---|
| Camera | Requested only if the app needs to take photos or videos. | Requested even if the app doesn’t use camera functionality. | Used to secretly record videos or take photos. |
| Contacts | Requested only if the app needs to access contact information. | Requested to steal user contact information. | Used for phishing attacks or spamming. |
| Location | Requested if location services are essential to app functionality. | Requested to track user movements without their knowledge. | Used for stalking or targeted advertising. |
| Storage | Requested to save user data or app files. | Requested to access and steal sensitive files. | Used to steal documents, photos, or financial data. |
User Education and Prevention Strategies
Source: wixstatic.com
Navigating the digital world, especially the app store landscape, requires a discerning eye. The proliferation of fake AI apps designed to mimic legitimate ones demands a proactive approach from users. Understanding how these scams operate and employing preventative measures is crucial to safeguarding your data and finances. This section Artikels practical strategies to help you identify and avoid falling victim to these fraudulent applications.
Protecting yourself from fake AI apps starts with a healthy dose of skepticism and a proactive approach to app verification. Don’t let flashy marketing or promises of groundbreaking AI features cloud your judgment. Remember, due diligence is your best defense.
Identifying and Avoiding Fake AI Applications
Recognizing a fake AI app isn’t always easy, but several red flags can tip you off. These range from suspicious app descriptions and developer information to concerning user reviews and unusual permissions requests. Being aware of these indicators can significantly reduce your risk.
For example, an app promising unrealistic results like “instant wealth” or “effortless weight loss” through AI should immediately raise suspicion. Similarly, apps with poorly written descriptions, grammatical errors, or inconsistent branding are often indicative of fraudulent activity. Always cross-reference the app’s information with the official website or social media pages of the purported developer.
Verifying App Authenticity Before Downloading, Chatgpt scams apple app store google play
A step-by-step approach to app verification can significantly reduce the chances of downloading a malicious application. This process involves checking several key aspects before you even consider tapping the “install” button.
- Verify the Developer: Research the app developer’s name. Look for a consistent presence online – a website, social media profiles, and contact information. Be wary of developers with limited or no online presence.
- Check App Reviews and Ratings: Thoroughly read user reviews and pay attention to both positive and negative feedback. A significant number of negative reviews citing issues like malware, data breaches, or deceptive practices should raise serious concerns. Look for patterns in negative reviews; are many users reporting the same problems?
- Examine App Permissions: Before installing, carefully review the permissions the app requests. An app requesting access to sensitive data like contacts, location, or financial information without a clear justification should be treated with extreme caution. Ask yourself: Does this app *really* need access to my contacts to function?
- Compare with Official Sources: If possible, compare the app’s information with the official website or social media pages of the company or organization that supposedly developed it. Discrepancies in branding, features, or contact information are major red flags.
The Importance of Reading App Reviews and Ratings
App store reviews are a treasure trove of user experiences, both positive and negative. They offer valuable insights into an app’s functionality, reliability, and potential risks. Don’t just look at the average rating; delve into the individual reviews to get a comprehensive picture.
Pay close attention to reviews that mention issues like unexpected charges, intrusive advertising, data breaches, or malware. A consistent pattern of negative feedback highlighting similar problems strongly suggests that the app may be malicious or poorly designed. A single negative review might be a fluke, but multiple consistent complaints should act as a warning signal.
Infographic: Key Warning Signs of Fraudulent Apps
Imagine an infographic with a bold, attention-grabbing title like “Spot a Fake App!”. The infographic would use a combination of visually striking icons and concise text. One section would depict a magnifying glass over a phone screen, highlighting the importance of verifying the developer’s information. Another section would show a red exclamation mark inside a broken padlock, representing suspicious permissions requests. A third section would display a user with a worried expression next to a phone with a pile of negative reviews, emphasizing the importance of checking user feedback. Finally, a section would show a dollar sign with a diagonal line through it, representing unexpected charges or financial risks. The color scheme would be predominantly red and yellow, colors commonly associated with warnings and danger, contrasted with a safe green for positive actions like verification.
Fake ChatGPT apps are flooding the Apple App Store and Google Play, preying on users’ AI curiosity. This manipulative tactic mirrors the spread of disinformation; remember the sheer volume of propaganda surrounding the Russia invaded Ukraine choice propaganda death conflict? These scams exploit trust just as effectively, highlighting the dangers of unchecked app distribution and the need for critical digital literacy.
Role of App Stores in Combating Fraud
Source: gadgetstouse.com
The responsibility for keeping app stores clean and safe from fraudulent applications rests squarely on the shoulders of Apple and Google. These tech giants control the gateways to billions of mobile devices, and their actions—or inactions—directly impact the security and financial well-being of countless users. The stakes are high, and the battle against fake AI apps and other malicious software is far from over.
The current review processes employed by Apple and Google vary, but both rely on a combination of automated checks and human review. Apple is often lauded for its stricter, more curated approach, leading to a reputation for a more secure App Store. Google Play, on the other hand, handles a significantly larger volume of apps, potentially leading to a higher rate of fraudulent apps slipping through the cracks. However, both platforms constantly update their algorithms and review processes, attempting to stay ahead of the ever-evolving tactics of malicious developers. Effectiveness, however, is a moving target, constantly challenged by new methods of deception.
Apple and Google’s Review Processes and Security Measures
Apple’s review process is known for its rigorousness, involving manual checks by human reviewers for compliance with App Store guidelines. This process, while thorough, can lead to longer wait times for app developers. Google Play’s automated systems play a more prominent role in its initial screening process, relying on machine learning to identify potential threats. This allows for faster app publication, but potentially at the cost of increased risk. Both platforms utilize various security measures, including sandboxing (restricting app access to system resources), code analysis, and malware detection software. However, these measures aren’t foolproof, and sophisticated malicious apps can often circumvent them.
Areas for Improvement in Combating Fake AI Apps
The rise of AI-powered apps has created a new frontier in app store fraud. Fake AI apps, often mimicking the functionality of legitimate AI tools, can trick users into downloading malware or revealing sensitive personal data. Both Apple and Google need to enhance their detection capabilities for these sophisticated scams. This includes improving the analysis of app code to identify potentially deceptive AI functionality and implementing more robust mechanisms for verifying the claims made by developers regarding their AI capabilities. Better collaboration with security researchers and AI specialists is also crucial to stay ahead of emerging threats.
Recommendations for Improving App Store Security
Significant improvements are needed to bolster the security of app stores and protect users. The following recommendations are critical:
- Implement more sophisticated AI-powered detection systems capable of identifying subtle signs of fraudulent activity, including sophisticated code obfuscation techniques used in fake AI apps.
- Increase the frequency and depth of app reviews, particularly for apps related to sensitive data or financial transactions.
- Develop a more transparent and accessible reporting mechanism for users to flag suspicious apps quickly and easily.
- Enhance collaboration with cybersecurity researchers and law enforcement agencies to share threat intelligence and coordinate responses to emerging threats.
- Strengthen developer verification processes, including stricter identity verification and background checks.
- Introduce a system of app reputation scores based on user reviews, security audits, and detection of malicious behavior.
- Develop clearer guidelines and stricter penalties for developers who create or distribute fraudulent apps.
Outcome Summary
The rise of fake AI apps on major app stores highlights a critical need for increased vigilance and stronger security measures. While app stores are working to combat these threats, individual users also bear the responsibility of protecting themselves. By staying informed, being skeptical, and following the safety tips Artikeld above, you can significantly reduce your risk of falling prey to these scams. Remember, a little caution can go a long way in the digital world.



