The hidden dangers of the decentralized web: Sounds like a sci-fi thriller, right? Wrong. It’s a very real and present threat. While the promise of a censorship-resistant, user-controlled internet is alluring, the decentralized web also harbors significant risks. From anonymity-fueled criminal activity to data breaches and the spread of misinformation, navigating this new frontier requires understanding its potential pitfalls. This isn’t about fear-mongering; it’s about informed participation.
We’ll dive into the complexities of anonymity’s dark side, exploring how it empowers malicious actors and challenges law enforcement. We’ll unpack the vulnerabilities of decentralized applications (dApps) and the difficulties in enforcing data protection in this new landscape. We’ll also examine the challenges of content moderation in a world without central authorities, the technical vulnerabilities ripe for exploitation, and the potential for exacerbating existing societal inequalities. Get ready to unpack the good, the bad, and the downright ugly of the decentralized web.
Anonymity and its Pitfalls
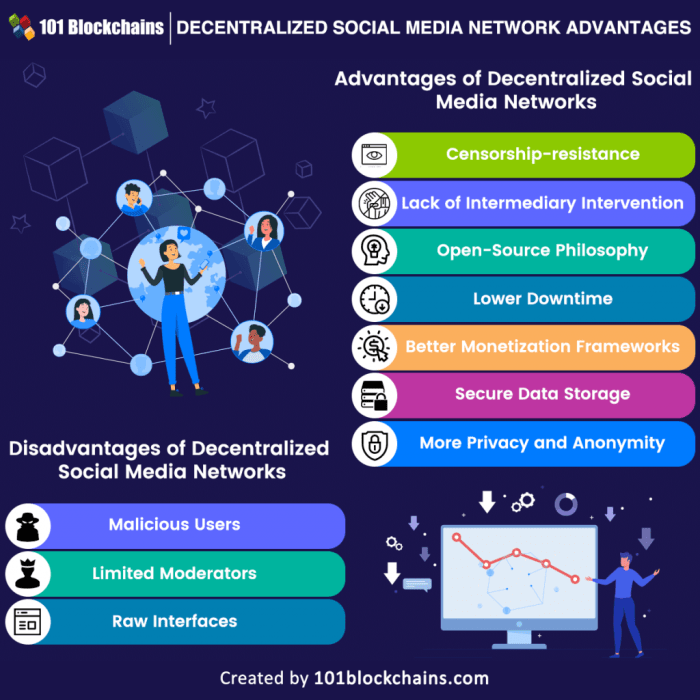
Source: 101blockchains.com
Navigating the decentralized web can be a minefield; outdated browsers are a prime example of the risks involved. The move by Microsoft to finally ditch Internet Explorer, as detailed in this article microsoft removing internet explorer from pcs , highlights the vulnerability of relying on legacy systems. This underscores the larger point: the decentralized web’s lack of centralized security updates leaves users exposed to a wider range of threats.
The decentralized web, while promising greater freedom and user control, presents a significant challenge: anonymity. While this can be beneficial for protecting privacy, it also creates fertile ground for illicit activities, making it difficult for law enforcement and potentially harming innocent users. The inherent difficulty in tracing actions back to individuals fuels a range of criminal enterprises, blurring the lines between legitimate and malicious online behavior.
The anonymity afforded by decentralized platforms significantly hampers law enforcement’s ability to investigate and prosecute crimes. Traditional methods of tracking IP addresses and user accounts are often ineffective, as decentralized networks lack central points of control. This makes tracing the source of malicious activities, such as hacking, data breaches, and the distribution of illegal content, extremely challenging, leading to a sense of impunity among perpetrators.
Increased Criminal Activity Facilitated by Anonymity
The cloak of anonymity empowers a surge in criminal activity on decentralized platforms. Scams and fraudulent schemes thrive in this environment, as perpetrators can easily create fake identities and disappear without a trace. The lack of accountability encourages the development of sophisticated scams, targeting unsuspecting users with promises of quick riches or other alluring offers. For example, the proliferation of fraudulent cryptocurrency investments and decentralized finance (DeFi) scams highlights the vulnerability of users to these schemes. These scams often involve complex smart contracts and decentralized exchanges, making it incredibly difficult to recover lost funds.
Exploitation of Pseudonymous Identities for Malicious Purposes
Pseudonymous identities, while offering a degree of privacy, are easily misused. Malicious actors can create numerous pseudonymous accounts to spread misinformation, harass individuals, or engage in coordinated attacks. Imagine a scenario where a group uses multiple pseudonymous accounts on a decentralized forum to manipulate public opinion, spread false information about a company, and then sell off their holdings of that company’s stock before the price plummets due to the negative publicity they themselves generated. The decentralized nature of the platform makes it extremely difficult to trace these actions back to the perpetrators, allowing them to operate with a significant degree of impunity.
Difficulty in Identifying Perpetrators of Crimes on Decentralized Platforms
Consider a hypothetical scenario: A user on a decentralized messaging platform receives a seemingly innocuous link. Clicking the link downloads malware onto their device, granting access to their personal information and financial accounts. Tracing the origin of the malicious link is challenging. The decentralized nature of the platform means there’s no central server to log the link’s creation or distribution. The perpetrator could be using a series of anonymizing tools and proxies, making it virtually impossible to identify their location or real identity. Even if the perpetrator’s pseudonymous account is identified, linking it to a real-world individual is an immense task requiring extensive forensic investigation, and even then, success is not guaranteed. The lack of centralized control and the reliance on cryptographic techniques make tracking down these perpetrators a complex and often unsuccessful endeavor.
Data Privacy and Security Risks
The decentralized web, while promising greater user control and transparency, presents significant challenges to data privacy and security. The very architecture designed to eliminate centralized points of failure also creates vulnerabilities that are difficult to address using traditional methods. This section explores the unique risks associated with data privacy and security on decentralized platforms, comparing them to their centralized counterparts and examining real-world examples.
Decentralized applications (dApps) often rely on blockchain technology, smart contracts, and distributed ledgers. While this distributed nature enhances resilience against single points of failure, it also complicates security and data protection. The lack of a central authority makes it challenging to implement and enforce consistent security protocols and data protection regulations. Furthermore, the open and transparent nature of many blockchain networks means that data, while not necessarily easily accessible, is often permanently recorded and potentially visible to anyone with the technical know-how.
Vulnerabilities of Decentralized Applications to Data Breaches and Hacks
The decentralized nature of dApps doesn’t inherently equate to impenetrable security. Smart contracts, the core logic of many dApps, can contain vulnerabilities that malicious actors can exploit. Bugs in the code, poorly designed access controls, or flawed cryptographic implementations can lead to significant data breaches or hacks. Moreover, the complexity of interacting with multiple nodes and potentially unknown third-party services increases the attack surface. Even seemingly minor flaws can have cascading effects across the entire decentralized network. Unlike centralized platforms, where a single point of failure can be quickly addressed, vulnerabilities in dApps can be harder to patch and require community consensus or extensive code upgrades, leaving the system exposed for longer periods.
Challenges of Enforcing Data Protection Regulations in the Decentralized Web Environment
Enforcing existing data protection regulations like GDPR or CCPA in the decentralized web environment is incredibly challenging. The absence of a central authority responsible for data governance makes it difficult to identify and hold accountable parties responsible for data breaches or violations. Furthermore, the global and borderless nature of many decentralized networks makes it challenging to apply national or regional regulations consistently. Tracing data flows and identifying data controllers or processors across a decentralized network requires significant technical expertise and international cooperation, which often proves difficult to achieve. The lack of clear legal frameworks specifically tailored to the decentralized web further exacerbates these challenges.
Comparison of Data Privacy Protections Offered by Centralized Versus Decentralized Platforms
Centralized platforms, while subject to their own security risks, typically offer more robust data protection mechanisms. They have established processes for data governance, compliance with regulations, and incident response. Centralized systems often employ sophisticated security measures such as firewalls, intrusion detection systems, and encryption protocols. In contrast, decentralized platforms generally lack these centralized control mechanisms, making data protection more reliant on the security practices of individual developers and users. While decentralization can enhance transparency and user control over data in certain aspects, it also shifts the burden of security and privacy to a much wider range of actors, leading to a potentially less secure and regulated environment.
Examples of Real-World Incidents Demonstrating Data Breaches or Privacy Violations on Decentralized Platforms
Several real-world incidents highlight the data privacy and security risks associated with decentralized platforms. While specific details and impact vary, these examples underscore the importance of robust security measures and responsible development practices in the decentralized web ecosystem.
| Incident | Platform | Impact | Mitigation Strategies |
|---|---|---|---|
| The DAO Hack (2016) | Ethereum | Loss of millions of dollars worth of ETH due to a smart contract vulnerability. | Improved smart contract auditing, security best practices for developers. |
| Poly Network Hack (2021) | Poly Network (cross-chain protocol) | Millions of dollars in various cryptocurrencies stolen due to vulnerabilities in multiple bridges. | Enhanced security audits, improved cross-chain communication security, better incident response plans. |
| Various DeFi exploits | Various DeFi platforms | Losses of user funds due to vulnerabilities in smart contracts and protocols. | Thorough code audits, robust security testing, improved risk management practices. |
| NFT marketplace scams | Various NFT marketplaces | Phishing scams, rug pulls, and fraudulent projects leading to financial losses and data breaches. | Improved user education, platform verification processes, stronger anti-fraud measures. |
Censorship Resistance and its Dark Side

Source: staderlabs.com
The decentralized web’s promise of censorship resistance is a double-edged sword. While it offers freedom from the control of single entities, it also creates a breeding ground for harmful content that traditional platforms actively combat. The lack of a central authority to moderate content presents unique challenges, forcing us to reconsider our approach to online safety and the very nature of digital communities.
The absence of centralized moderation mechanisms on decentralized platforms allows for the unchecked proliferation of misinformation, hate speech, and illegal activities. Unlike centralized platforms that can swiftly remove problematic content, decentralized systems often lack efficient methods for identifying and addressing such issues. This creates an environment where harmful ideologies can spread rapidly, potentially radicalizing individuals and undermining public trust in information sources.
The Spread of Misinformation and Hate Speech
The decentralized nature of these platforms makes it difficult to track and remove false or misleading information. The inherent anonymity often associated with these systems allows individuals to spread harmful narratives without fear of immediate repercussions. For example, conspiracy theories and disinformation campaigns can flourish unchecked, impacting public health, political processes, and social cohesion. The lack of a clear reporting mechanism and the difficulty in identifying perpetrators further exacerbate the problem. While some decentralized platforms attempt to implement community-based moderation, these efforts often prove insufficient to deal with the sheer volume and sophistication of harmful content. The decentralized structure makes it harder to coordinate action and apply consistent standards.
Combating Online Harassment and Abuse in Decentralized Environments
Online harassment and abuse thrive in environments lacking robust moderation. The anonymity and decentralized nature of these platforms make it challenging to identify and hold perpetrators accountable. Victims often lack effective recourse, leading to increased vulnerability and a chilling effect on free expression. While some decentralized platforms are exploring solutions like blockchain-based reputation systems, these are still in their early stages of development and their effectiveness remains to be seen. The lack of a clear chain of command and a consistent enforcement mechanism makes it difficult to address the issue comprehensively. The challenge lies in balancing censorship resistance with the need to protect vulnerable users from harm.
Content Moderation: Centralized vs. Decentralized
Centralized platforms, such as Facebook or Twitter, employ a hierarchical system of content moderation. They utilize a combination of automated tools and human moderators to identify and remove violating content. This approach, while not without its flaws, offers a relatively swift and efficient response to harmful content. In contrast, decentralized platforms rely heavily on community-based moderation or on-chain governance mechanisms. These methods are often slower, less efficient, and more prone to inconsistencies. The lack of a single point of control makes it difficult to establish and enforce clear content policies. The comparison highlights the trade-off between censorship resistance and the need for effective content moderation. While decentralized systems offer greater freedom from centralized control, they often lack the mechanisms necessary to prevent the spread of harmful content effectively.
Technical Vulnerabilities and Exploits: The Hidden Dangers Of The Decentralized Web
The decentralized web, while promising increased security and freedom, isn’t immune to vulnerabilities. The very technologies designed to enhance privacy and resistance to censorship can also become avenues for exploitation, creating significant risks for users and developers alike. Understanding these weaknesses is crucial for navigating the decentralized landscape safely.
Smart contracts, the backbone of many decentralized applications (dApps), are essentially self-executing contracts with the code written directly into the blockchain. While this offers automation and transparency, it also introduces a significant vulnerability: bugs in the code can be exploited for malicious purposes. Similarly, decentralized storage solutions, while promising data resilience and censorship resistance, present their own unique set of security challenges.
Smart Contract Vulnerabilities, The hidden dangers of the decentralized web
The immutability of blockchain technology, while a strength, also means that flawed smart contracts cannot be easily patched. A single coding error can lead to significant financial losses or allow malicious actors to drain funds or manipulate the system. The infamous DAO hack in 2016, where a vulnerability in the DAO smart contract allowed attackers to steal millions of dollars worth of ETH, serves as a stark reminder of the potential consequences. This exploit highlighted the importance of rigorous code audits and security best practices in smart contract development. Further examples include reentrancy attacks, where a malicious contract can repeatedly call a function within another contract to drain funds, and overflow/underflow errors, where numerical calculations exceed the limits of the data type, leading to unexpected behavior.
Decentralized Storage Risks
Decentralized storage solutions like IPFS (InterPlanetary File System) offer a compelling alternative to centralized cloud storage, promising data resilience and censorship resistance. However, the decentralized nature of these systems also introduces security challenges. Data stored on IPFS is not inherently encrypted; it’s the responsibility of the user to encrypt sensitive information before uploading it. Furthermore, while IPFS aims to make data highly available, there’s no guarantee of its permanence. If the nodes hosting a particular piece of data go offline, that data becomes inaccessible. Additionally, the decentralized nature makes it difficult to track down malicious actors who might tamper with or delete data.
Examples of Vulnerabilities and Exploits
Several high-profile incidents have exposed vulnerabilities in popular decentralized technologies. The Parity multi-sig wallet bug in 2017 resulted in the loss of millions of dollars worth of ETH due to a coding error. The vulnerability allowed a single user to freeze funds belonging to many others. This event demonstrated the critical need for thorough testing and security audits of even established projects. Another example involves vulnerabilities discovered in various DeFi (Decentralized Finance) protocols, often leading to flash loan attacks, where attackers borrow large sums of cryptocurrency to manipulate prices and profit from arbitrage opportunities before returning the loan.
Types of Attacks Targeting Decentralized Systems
| Attack Type | Impact | Mitigation Strategies | Example |
|---|---|---|---|
| Smart Contract Exploits (e.g., reentrancy) | Loss of funds, system manipulation | Formal verification, rigorous code audits, security testing | The DAO hack |
| Sybil Attacks | Compromised consensus, manipulation of voting or governance | Reputation systems, identity verification, Proof-of-Stake mechanisms | Manipulating voting in a decentralized autonomous organization (DAO) |
| Denial-of-Service (DoS) Attacks | Unavailability of services, network congestion | Redundant infrastructure, distributed network architecture, rate limiting | Overwhelming a blockchain network with transactions |
| Data Tampering | Compromised data integrity, misinformation | Data encryption, cryptographic hashing, blockchain immutability (where applicable) | Altering data stored on IPFS |
Accessibility and Inclusivity Issues
The decentralized web, while promising freedom and autonomy, presents a significant challenge to accessibility and inclusivity. Its very nature, built on complex technologies and often lacking centralized control, can inadvertently create barriers for a large segment of the population, exacerbating existing digital divides and potentially fostering discriminatory practices. The promise of a truly open web risks becoming an exclusive club if careful consideration isn’t given to the needs of all users.
The decentralized web’s reliance on technical expertise poses a considerable hurdle for individuals with limited digital literacy. Many decentralized applications (dApps) require a level of understanding of cryptography, blockchain technology, and command-line interfaces that are beyond the capabilities of the average internet user. This technical barrier effectively shuts out a significant portion of the population, particularly older adults, those with disabilities, and individuals from lower socioeconomic backgrounds who may lack access to the necessary training and resources. This digital divide is further widened by the lack of user-friendly interfaces and intuitive navigation common in centralized platforms.
Technical Barriers to Access for Users with Limited Technical Skills
Navigating the decentralized web often involves interacting with complex interfaces and understanding technical concepts. For example, managing cryptocurrency wallets, interacting with smart contracts, and understanding the nuances of decentralized identity systems requires a significant level of technical proficiency. The lack of readily available, accessible tutorials and support resources further compounds this problem. Many existing resources are geared towards a technically savvy audience, leaving less tech-proficient users struggling to understand and participate. This lack of accessible resources leads to a significant barrier to entry for a large portion of the population. The decentralized web, in its current form, inadvertently excludes individuals who lack the technical expertise to participate effectively.
Potential for Discriminatory Practices on Decentralized Platforms
Decentralized platforms, while aiming for censorship resistance, are not immune to discriminatory practices. The lack of centralized oversight and moderation can allow harmful content and discriminatory actions to proliferate unchecked. For instance, algorithms used in decentralized systems for content moderation or access control could inadvertently perpetuate biases present in the training data, leading to unfair or discriminatory outcomes. Furthermore, the anonymity afforded by some decentralized platforms can embolden individuals to engage in hateful speech or discriminatory behavior without fear of immediate repercussions. The absence of robust reporting mechanisms and effective enforcement further contributes to this problem. A decentralized system, without proper governance and moderation, risks becoming a breeding ground for discrimination.
Accessibility Challenges for Users with Disabilities
Imagine Sarah, a visually impaired individual, attempting to access information on a decentralized platform. While the platform may boast censorship resistance and data privacy, it lacks features like screen reader compatibility and alternative text for images. Navigating the platform becomes a significant challenge, as she relies on screen readers to interpret the information. The lack of structured data and semantic HTML further exacerbates this problem, making it impossible for her screen reader to accurately convey the information presented. Similarly, a user with motor impairments might find it difficult to interact with the platform’s complex interface, which lacks keyboard navigation and other assistive technology support. The decentralized web, without a commitment to accessibility standards, effectively excludes users with disabilities from accessing information and participating fully.
The Rise of Decentralized Autonomous Organizations (DAOs) and Associated Risks
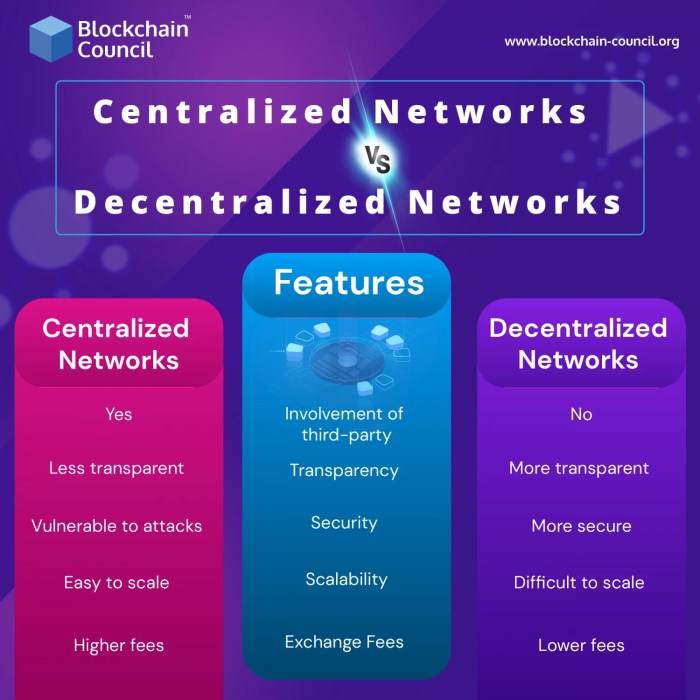
Source: blockchain-council.org
Decentralized Autonomous Organizations (DAOs) are buzzing – they represent a bold new experiment in organizational structure, promising transparency, efficiency, and community governance. But this brave new world isn’t without its shadows. The very features that make DAOs attractive also introduce unique and significant risks, requiring careful consideration before diving in. Let’s explore some of the key challenges.
Governance Issues and Conflicts of Interest within DAOs
DAOs function based on pre-programmed rules encoded in smart contracts. While this aims for objectivity, it doesn’t eliminate the potential for conflict. Token holders, the DAO’s members, might have differing agendas, leading to disagreements on strategic direction or resource allocation. Imagine a DAO developing a new cryptocurrency; some members might prioritize rapid expansion, while others might focus on security, leading to potential clashes and inefficient decision-making. Furthermore, conflicts of interest can arise if individuals or groups hold significant influence within the DAO while simultaneously benefiting from decisions that might not be in the best interest of the entire organization. The lack of centralized control makes resolving these conflicts challenging, relying heavily on the community’s ability to reach consensus, a process that can be slow and prone to manipulation.
Legal and Regulatory Challenges Posed by DAOs
The decentralized and borderless nature of DAOs poses significant legal and regulatory headaches. Questions surrounding liability, taxation, and jurisdiction are far from settled. Who is responsible if a DAO’s smart contract contains a flaw that leads to financial losses for its members? Which legal system governs a DAO operating across multiple countries? These uncertainties create legal ambiguity that can deter participation and investment, and potentially expose members to significant financial and legal risks. The regulatory landscape is constantly evolving, and navigating this uncertainty requires careful legal counsel and a thorough understanding of the relevant laws in different jurisdictions.
Real-World Scenarios Highlighting Risks Associated with DAOs
Several real-world examples illustrate the potential pitfalls of DAOs. The infamous “The DAO” hack in 2016, where millions of dollars worth of ether were stolen due to a vulnerability in its smart contract, remains a cautionary tale. This event highlighted the significant security risks associated with poorly designed or audited smart contracts. Other examples include governance disputes where disagreements over the DAO’s direction led to internal fracturing and loss of value. These instances underscore the importance of thorough due diligence, robust security measures, and a well-defined governance structure before participating in a DAO.
Best Practices for Mitigating Risks Associated with Participation in DAOs
Participating in a DAO should be approached with caution and thorough research. Before investing time or resources, thoroughly vet the DAO’s smart contracts – ideally through independent audits. Understand the DAO’s governance structure, ensuring it’s transparent and fair. Diversify your investments to minimize risk. Actively participate in the DAO’s community forums to stay informed and contribute to decision-making. Finally, remember that no investment is risk-free; understand the potential downsides before committing. Treat DAO participation like any other investment: do your homework, and don’t invest more than you can afford to lose.
Outcome Summary
The decentralized web presents a double-edged sword. Its promise of freedom and autonomy is undeniable, but ignoring the inherent risks is reckless. Understanding the challenges related to anonymity, data privacy, content moderation, technical vulnerabilities, and accessibility is crucial for responsible engagement. As this technology evolves, so must our awareness of its potential downsides. The future of the internet may be decentralized, but our approach to it must be informed and cautious. Let’s navigate this new frontier wisely, leveraging its benefits while mitigating its dangers.
